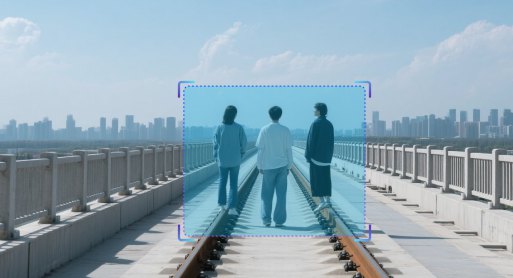
Stranger Detection

Algorithm Introduction
This AI-powered vision recognition algorithm extracts facial feature vectors from surveillance video streams or captured images, storing them in a spatiotemporal trajectory database to enable retrospective tracking and identity verification of unknown individuals. The system supports multi-dimensional facial attribute recognition, including gender, age, mask color, eyewear detection, hat styles, and facial hair patterns, facilitating applications in urban security operations, intelligent surveillance deployment, and high-risk individual analysis.
Application Value
-

Urban Operations Center
The algorithm conducts structured identification and data retention of unfamiliar individuals at public access points. This supports incident tracking and surveillance analysis for security operations. -

Big Data Center
The algorithm establishes spatiotemporal facial database to enable cross-temporal person comparison and early warning model development. -

Industrial Park
The algorithm detects unauthorized unfamiliar faces entering the facility. This enhances intrusion prevention and anomaly detection capabilities.
FAQ
-
Algorithm AccuracyAll algorithms published on the website claim accuracies above 90 %. However, real-world performance drops can occur for the following reasons:
(1) Poor imaging quality, such as
• Strong light, backlight, nighttime, rain, snow, or fog degrading image quality
• Low resolution, motion blur, lens contamination, compression artifacts, or sensor noise
• Targets being partially or fully occluded (common in object detection, tracking, and pose estimation)
(2) The website provides two broad classes of algorithms: general-purpose and long-tail (rare scenes, uncommon object categories, or insufficient training data). Long-tail algorithms typically exhibit weaker generalization.
(3) Accuracy is not guaranteed in boundary or extreme scenarios.
-
Deployment & InferenceWe offer multiple deployment formats—Models, Applets and SDKs.
Compatibility has been verified with more than ten domestic chip vendors, including Huawei Ascend, Iluvatar, and Denglin, ensuring full support for China-made CPUs, GPUs, and NPUs to meet high-grade IT innovation requirements.
For each hardware configuration, we select and deploy a high-accuracy model whose parameter count is optimally matched to the available compute power.
-
How to Customize an AlgorithmAll algorithms showcased on the website come with ready-to-use models and corresponding application examples. If you need further optimization or customization, choose one of the following paths:
(1) Standard Customization (highest accuracy, longer lead time)
Requirements discussion → collect valid data (≥1 000 images or ≥100 video clips from your scenario) → custom algorithm development & deployment → acceptance testing
(2) Rapid Implementation (Monolith:https://monolith.sensefoundry.cn/)
Monolith provides an intuitive, web-based interface that requires no deep AI expertise. In as little as 30 minutes you can upload data, leverage smart annotation, train, and deploy a high-performance vision model end-to-end—dramatically shortening the algorithm production cycle.